Preimage assaults. MD5 is vulnerable to preimage attacks, where by an attacker can find an enter that hashes to a specific worth. This power to reverse-engineer a hash weakens MD5’s usefulness in shielding delicate details.MD5 is still being used these days like a hash perform Despite the fact that it has been exploited For a long time. In the fo
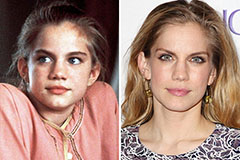 Anna Chlumsky Then & Now!
Anna Chlumsky Then & Now! Molly Ringwald Then & Now!
Molly Ringwald Then & Now! Kelly Le Brock Then & Now!
Kelly Le Brock Then & Now! Nancy Kerrigan Then & Now!
Nancy Kerrigan Then & Now! Tina Majorino Then & Now!
Tina Majorino Then & Now!